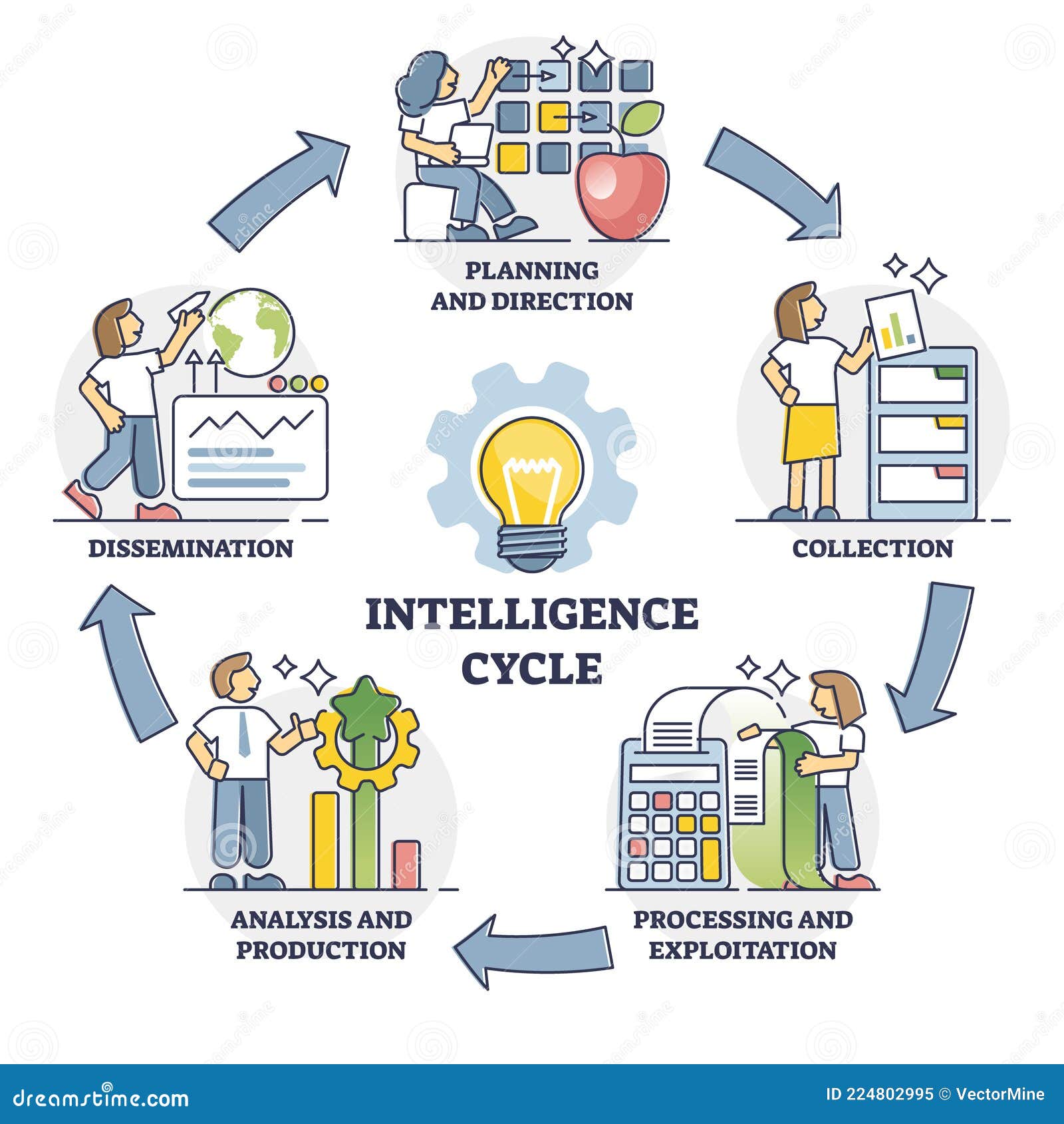
Intelligence Cycle with Labeled Information Processing Steps Outline Diagram Stock Vector - Illustration of processing, direction: 224802995

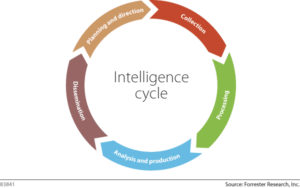
Intelligence Process, -Step Intelligence Process - Crime and intelligence analysis: an integrated real-time approach
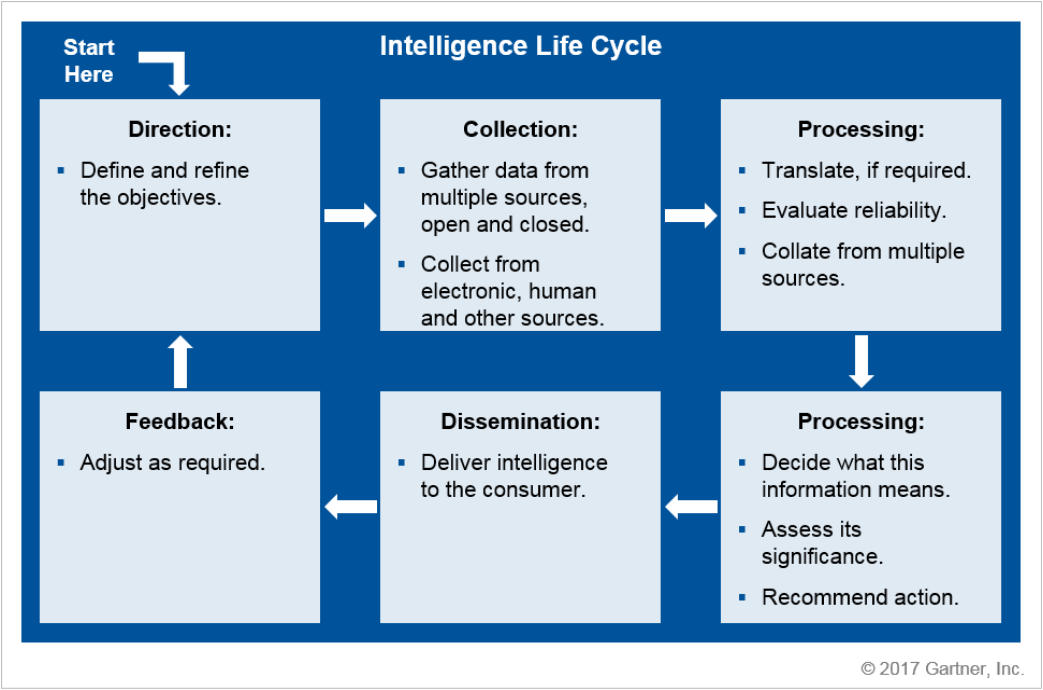
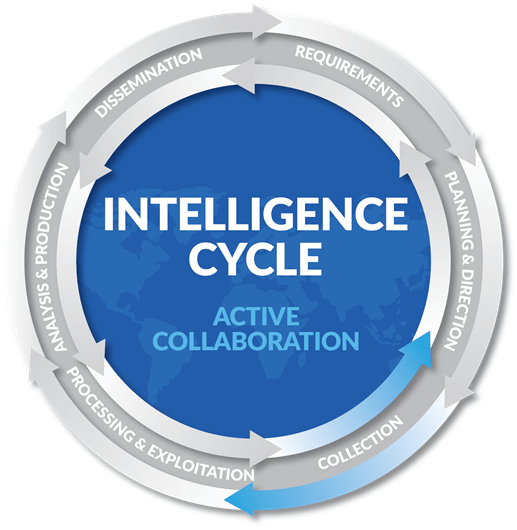
5 Practical Steps for Leveling Up Your Threat Intelligence - Malware News - Malware Analysis, News and Indicators
The Intelligence Cycle: An Introduction to Direction, Collection, Analysis & Dissemination of Intelligence

![2. The Threat Intelligence Cycle - Threat Intelligence in Practice [Book] 2. The Threat Intelligence Cycle - Threat Intelligence in Practice [Book]](https://www.oreilly.com/library/view/threat-intelligence-in/9781492049302/assets/tiip_0201.png)


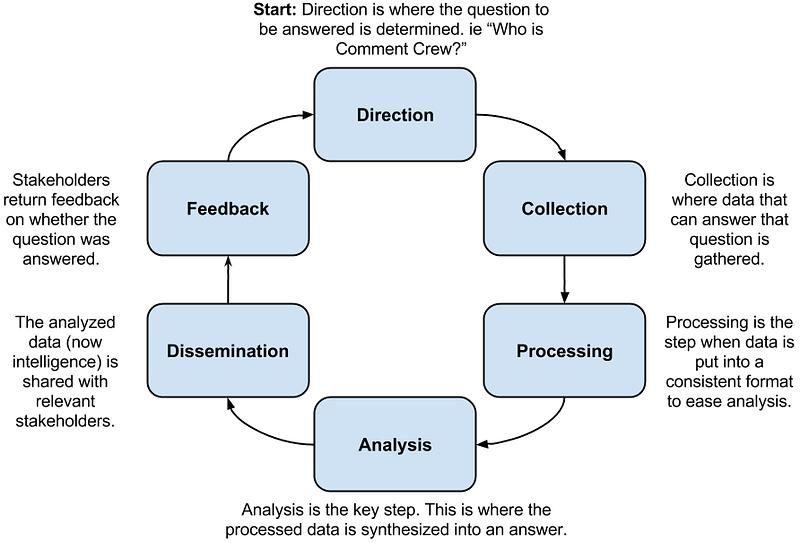
![The intelligence cycle steps - Practical Cyber Intelligence [Book] The intelligence cycle steps - Practical Cyber Intelligence [Book]](https://www.oreilly.com/library/view/practical-cyber-intelligence/9781788625562/assets/fea11dae-29bc-4b01-b4d6-b6c4c5999b5b.png)